Introduction
Organised crime is no longer confined to darkened back alleys or whispered deals in underground establishments. In the twenty-first century, criminal syndicates operate with corporate-like precision spanning continents, exploiting digital infrastructure, and evading conventional law enforcement with alarming sophistication. Drug trafficking, human trafficking, cybercrime, money laundering, and terrorism financing have all evolved into intricately networked enterprises. Against this backdrop, the law enforcement community has turned to technology not merely as an aid, but as an indispensable weapon.
This blog explores the multifaceted role of technology in investigating organised crime — its legal underpinnings, practical applications, and the ethical tensions it necessarily raises.
I. Defining Organised Crime: A Legal Perspective
Before examining technology’s role, it is essential to understand what organised crime legally constitutes. Under the United Nations Convention against Transnational Organized Crime (UNTOC), 2000 , also known as the Palermo Convention an “organised criminal group” is defined as a structured group of three or more persons, existing for a period of time and acting in concert with the aim of committing one or more serious crimes for financial or other material benefit.
In India, the Maharashtra Control of Organised Crime Act, 1999 (MCOCA) and provisions under the Unlawful Activities (Prevention) Act, 1967 (UAPA) address organised criminal activity. These statutes collectively recognise the structured, hierarchical nature of such crimes, making their investigation a complex, resource-intensive endeavour one where technology becomes a critical equaliser.
II. Surveillance Technologies: Watching the Watchers
Among the most widely deployed investigative technologies are surveillance systems. Closed-circuit television (CCTV) networks, Automatic Number Plate Recognition (ANPR) systems, and drone surveillance have transformed the capacity of law enforcement to monitor suspects and gather evidence in real time.
In India, the Supreme Court has consistently grappled with the balance between surveillance and the right to privacy, particularly post the landmark judgment in Justice K.S. Puttaswamy (Retd.) v. Union of India (2017), where a nine-judge bench unanimously held that the right to privacy is a fundamental right under Article 21. This ruling has significant implications for surveillance-based investigations evidence gathered through disproportionate or unlawful surveillance may be challenged on constitutional grounds. Nevertheless, lawfully authorised interception under the Indian Telegraph Act, 1885 and the Information Technology Act, 2000 remains a cornerstone of organised crime investigations.
III. Digital Forensics and Cyber Intelligence
Organised crime syndicates have increasingly migrated their operations to the digital realm using encrypted messaging platforms, the dark web, and cryptocurrency to coordinate and fund activities. Digital forensics has therefore become a critical investigative discipline.
Digital forensic investigators employ specialised tools such as Cellebrite (for mobile device extraction), EnCase, and FTK (Forensic Toolkit) to recover deleted files, trace communications, and reconstruct timelines of criminal activity. The admissibility of such electronic evidence in Indian courts is governed by Sections 65A and 65B of the Indian Evidence Act, 1872, which require a certificate of authenticity from a competent authority as a prerequisite to admission.
Blockchain analytics tools such as Chainalysis and Elliptic have emerged as powerful instruments in tracing cryptocurrency transactions linked to money laundering and drug trafficking. Given that financial flows are the lifeblood of organised crime, disrupting these channels through technological surveillance strikes at the very heart of criminal enterprises.
IV. Artificial Intelligence and Predictive Policing
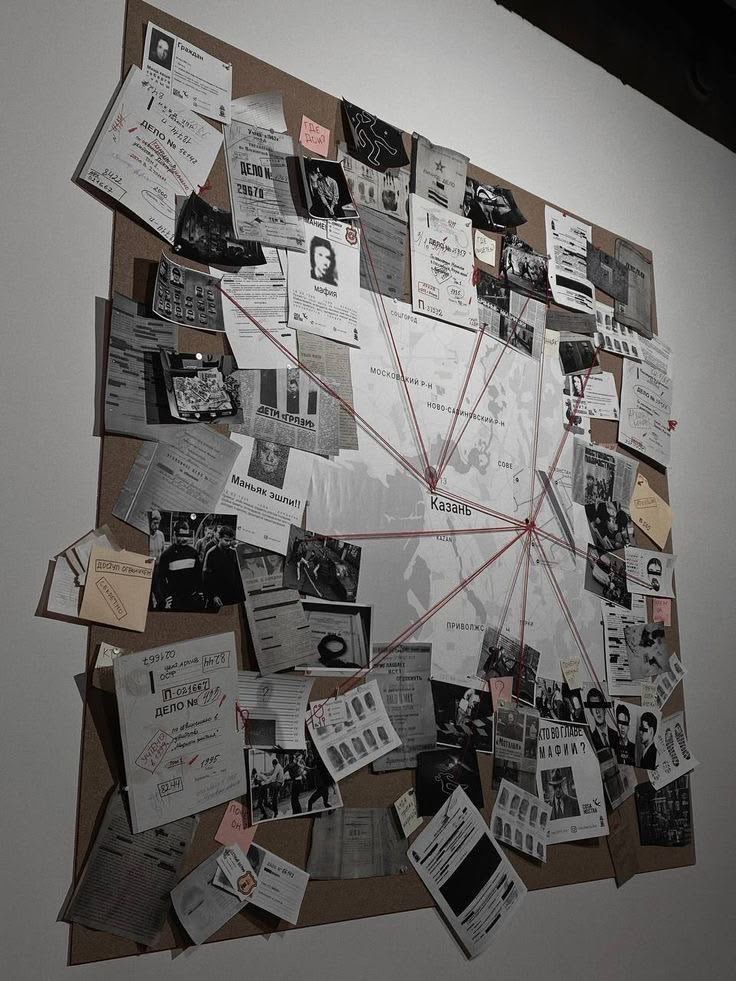
Artificial Intelligence (AI) and machine learning algorithms are reshaping the investigative landscape. Predictive policing platforms analyse historical crime data, geographic patterns, and social network analysis to identify potential criminal hotspots and flag high-risk individuals. In the context of organised crime, social network analysis (SNA) tools map the relationships between suspects, identifying key operatives, financiers, and logistical coordinators within criminal hierarchies.
However, AI-driven policing raises profound legal concerns. Algorithmic bias — where systems replicate and amplify existing prejudices embedded in historical data — can lead to discriminatory targeting of marginalised communities. The absence of a comprehensive regulatory framework governing AI in policing in India leaves these tools largely unchecked, necessitating urgent legislative attention. A purely technology-dependent approach risks undermining due process and the presumption of innocence, principles enshrined in Articles 20 and 21 of the Constitution.
V. Interagency Cooperation and Shared Intelligence Platforms
Organised crime, by its transnational nature, demands coordinated responses across jurisdictions. Technology facilitates this through shared intelligence platforms such as Interpol’s I-24/7 secure global communications network and UNODC’s GoAML platform for financial intelligence sharing. In India, the Crime and Criminal Tracking Network and Systems (CCTNS) project seeks to digitise and interconnect police records across states, enabling more efficient tracking of organised criminal networks.
Mutual Legal Assistance Treaties (MLATs) further enable cross-border evidence sharing in digital investigations, though the pace of international cooperation often lags behind the speed at which criminal networks operate a gap that technology platforms increasingly endeavour to bridge.
VI. The Legal and Ethical Crossroads
The deployment of technology in criminal investigations is not without its tensions. The use of spyware such as Pegasus controversially deployed against journalists, activists, and politicians illustrates the potential for abuse when surveillance technology operates in a legal vacuum. The debate around end-to-end encryption further illustrates the dilemma: while it protects legitimate privacy interests, it also shields criminal communications from lawful interception.
Judicial oversight, therefore, is non-negotiable. Technology-enabled investigations must remain anchored in the rule of law authorised by judicial warrant where required, subject to oversight mechanisms, and respectful of constitutional guarantees. The Personal Data Protection Bill (now subsumed into the Digital Personal Data Protection Act, 2023) marks a step forward in regulating data-driven surveillance, though its full implications for law enforcement are yet to be tested.
Conclusion
Technology has irrevocably transformed the investigation of organised crime. From digital forensics to AI-driven analytics and blockchain tracing, law enforcement agencies now wield tools of unprecedented power. Yet power, as both philosophy and law remind us, demands accountability.
The challenge for the legal system is not merely to keep pace with technological innovation, but to shape its deployment through robust legal frameworks that uphold civil liberties while enabling effective criminal justice. The digital shield against organised crime must be wielded with both strength and restraint for a democracy that sacrifices its fundamental rights in the name of security ultimately undermines the very foundations it seeks to protect.
References:
- https://www.unodc.org/documents/organized-crime/LawEnforcement/Electronic_surveillance.pdf
- United States Congress Committee on Energy and Commerce, Committee Opens Investigation into Warrantless Wiretapping http://energycommerce.house.gov/Press_110/110nr98.shtml (accessed 5 February 2009)
-
Transnational Crime and Technology
-
“PROTON: Modelling the Processes Leading to Organised Crime and Terrorist Networks,” Transcrime (Università Cattolica del Sacro Cuore), March 11, 2024
PROTON
- https://theacademic.in/wp-content/uploads/2025/03/62.pdf