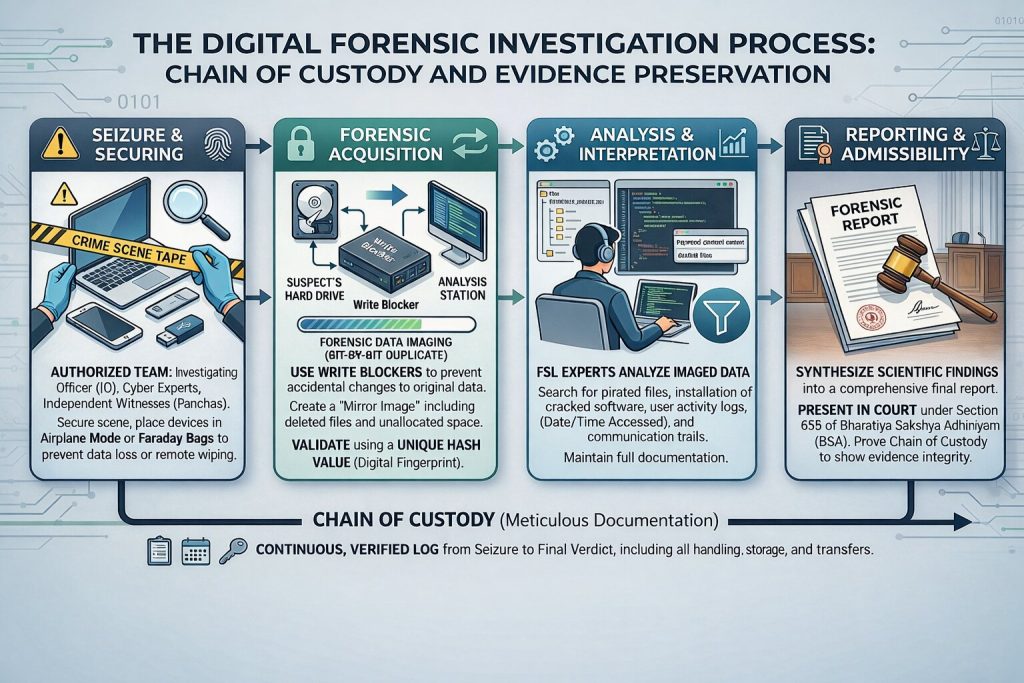
In the realm of modern law enforcement, the Digital Forensic Investigation Process serves as the backbone of cybercrime prosecution, transforming volatile electronic data into stable, court-admissible evidence. At the heart of this process lie the twin pillars of the Chain of Custody and Evidence Preservation.
The Chain of Custody acts as a meticulous, unbroken paper trail that documents every person who handled a piece of evidence, from the moment of seizure to its presentation in court, ensuring no unauthorized access or tampering occurred.
Simultaneously, Evidence Preservation utilizes advanced technical protocols—such as forensic imaging and write-blocking—to freeze data in its original state, protecting its integrity against the silent risks of accidental modification or remote wiping. Together, these protocols ensure that the “digital truth” uncovered by investigators remains beyond reproach under the scrutiny of the judicial system.
Everyday Examples
|
Type of Content |
What Piracy Looks Like |
Real-Life Example |
|
Movies |
Watching or downloading from illegal websites |
Watching a new Bollywood release on a free site instead of going to the cinema or using a legal app |
|
Software |
Using cracked versions or fake license keys |
Installing Photoshop using a YouTube tutorial that bypasses payment |
|
Books & PDFs |
Sharing copyrighted books without permission |
Forwarding a paid textbook PDF to friends on WhatsApp |
|
Music & Games |
Downloading from unofficial sources |
Getting a new game from a random link instead of the Play Store or App Store |
Why It’s a Problem
Harms creators: Artists, authors, and developers lose income and recognition for their work.
Breaks the law: Digital piracy violates copyright rules and can result in fines or even jail time.
Puts you at risk: Pirated files often contain viruses, malware, or hidden threats that can damage your device or steal your data.
What You Can Do Instead
Choose trusted platforms: Watch, read, or listen using legal services like Netflix, Spotify, or Kindle.
Get software the right way: Buy or rent apps and games from official stores like Google Play or Microsoft Store.
Respect creators: Pay for content to support the people who made it.
Notable Examples in India
Tamilrockers: A notorious website known for leaking new films within hours of their theatrical release. The site frequently changes its domain name to evade bans.
Telegram Groups: Numerous groups on this platform illegally distribute paid content from OTT services like Netflix and Amazon Prime.
Software Piracy: The illegal use of pirated software, including Microsoft Office, Windows, and Adobe products, is widespread in cybercafés and small businesses.
The Impact of Piracy on the Indian Film Industry
Financial Drain: The Indian film industry suffers an annual loss of thousands of crores due to piracy.
Harm to Creators: Artists, producers, and writers are denied their rightful earnings, stifling creativity and investment.
Cybersecurity Threats: Downloading pirated content exposes users to significant risks, as these files often contain malware and viruses.
Market Distortion: Legal streaming services and production houses face unfair competition from pirated content, which disrupts the legitimate market.
India’s Legal Framework Against Digital Piracy
India has developed a multi-pronged legal approach to combat digital piracy, combining copyright law, cyber regulations, and specific provisions targeting film piracy.
Copyright Act, 1957
This is the cornerstone of India’s copyright protection regime.
Section 51 – When Copyright is Infringed:
|
Clause |
What the Law Says |
Example |
Possible Legal Consequences |
|
51(a)(i) |
Doing any act which only the copyright owner is allowed to do, without permission. |
Copying a novel and selling it; making an unauthorised movie remake; recording a song without a licence. |
Civil suit for damages; criminal prosecution under Section 63 (up to 3 years jail + fine). |
|
51(a)(ii) |
Permitting any place to be used for infringement, knowing it will be used for such purpose. |
Renting out a hall to screen a pirated movie; letting your shop be used to sell counterfeit books. |
Fine; imprisonment; closure of premises by court order. |
|
51(b)(i) |
Selling, letting for hire, or offering infringing copies for sale/hire. |
Selling pirated DVDs or photocopied textbooks. |
Seizure of goods; damages; imprisonment. |
|
51(b)(ii) |
Distributing infringing copies for trade/business to prejudice the owner. |
Distributing fake software CDs to customers. |
Criminal charges; monetary penalties. |
|
51(b)(iii) |
Exhibiting infringing copies in public for trade/business. |
Public screening of a pirated film at a café. |
Fines; possible jail term. |
|
51(b)(iv) |
Importing infringing copies into India (except for personal use). |
Importing 500 pirated game discs from another country for sale. |
Customs seizure; legal action by copyright owner. |
The Nuance: In India, downloading a single movie for your own private viewing is rarely prosecuted. However, the moment you upload (like on BitTorrent) or share (like in a WhatsApp group), you move from “personal use” to “distribution,” which triggers the heavy criminal penalties you listed.
Section 63 & 65A: Sections 63 and 65A of the Copyright Act outline penalties for infringement, including imprisonment and monetary fines. Section 65A specifically targets offenses related to the circumvention of technological protection measures applied to copyrighted works.
Section 65B: The Copyright Act has special rules to stop people from illegally copying things using technology. Section 65B specifically makes it illegal to get around Technological Protection Measures (TPMs), which are like digital locks put on movies or music to prevent copying. By making it an offense to bypass these locks, the law protects creators and their work in the digital world. For instance, if you use a special program to break the copy protection on a movie disc so you can make a free copy, you would be breaking this law.
For investigating and prosecuting such crimes, the Bharatiya Nagarik Suraksha Sanhita (BNSS) plays a vital role, with provisions like Sections 102, 103, and 185 empowering law enforcement to issue search warrants and conduct searches to seize pirated materials and related devices. The Bharatiya Sakshya Adhiniyam (BSA) ensures that such evidence is admissible in court, with Section 63 specifically providing the legal basis for admitting electronic and digital records – such as hard drives, emails, or server logs – in piracy cases.
The Information Technology Act, 2000
The Information Technology (IT) Act, 2000 works alongside the Copyright Act to combat digital piracy. While the Copyright Act focuses on the intellectual property itself, the IT Act targets the technology-based crimes involved.
Section 43(b) makes it a civil offense to illegally download or copy digital data without permission, allowing for compensation to be paid to the victim.
Section 66 makes such an act a criminal offense if it is done “dishonestly or fraudulently,” with the potential for imprisonment and fines.
By doing so, the IT Act provides a legal framework to prosecute those who use computers and networks to illegally access, copy, or distribute copyrighted material.
Cinematograph (Amendment) Act, 2023
The Cinematograph (Amendment) Act, 2023 is a new law specifically designed to stop movie piracy. It adds a powerful tool to combat the illegal recording and distribution of films.
Key Provisions
The main change is Section 6AA, which makes it a criminal offense to illegally record, transmit, or broadcast a movie, or any part of it. This directly targets practices like camcording (recording a movie in a theatre with a camera) and other unauthorized ways of capturing and sharing films.
This amendment shows that the government is serious about protecting the entertainment industry from piracy, particularly in movie theatres and on streaming platforms.
Landmark Legal Cases
Several key legal cases in India have strengthened the enforcement of copyright law in the digital age.
MySpace Inc. v. Super Cassettes Industries Ltd. (2011): In a significant ruling, the Delhi High Court established that online platforms are responsible for removing pirated content as soon as they are notified by the copyright holder. This case set a precedent for the “notice-and-takedown” principle in India.
Viacom18 Media Pvt. Ltd. v. Movierulz.tv (2019): This case marked a major step forward by introducing the concept of a “dynamic injunction.” The court ordered Internet Service Providers (ISPs) to not only block specific piracy websites but also to proactively block any new “mirror” sites that pop up in the future.
Eros International v. BSNL (2016): The Bombay High Court’s decision in this case further reinforced the duty of ISPs. The court ordered BSNL and other ISPs to block websites that were illegally leaking Eros films, thereby confirming that ISPs have a legal responsibility to prevent access to infringing content.
John Doe” orders (also known as Ashok Kumar orders) are frequently used in India to block anonymous pirate sites before a big movie release.
Government Initiatives to Combat Piracy
The Indian government has launched several initiatives to combat digital piracy.
National Cyber Crime Reporting Portal: The government provides a dedicated online portal where citizens can easily report instances of piracy and other cybercrimes.
Website Blocking: Indian courts and the Ministry of Electronics & IT actively order Internet Service Providers (ISPs) to block websites that are known for distributing pirated content.
Awareness Campaigns: The government supports and collaborates with industry bodies like the Film Federation of India to run public campaigns that educate people on the harms of piracy and the importance of respecting copyright.
Preventive Measures & Recommendations
To effectively combat digital piracy, a multi-pronged approach is necessary, combining legal, technological, and educational strategies.
Technological Safeguards: Implementing strong technical measures is crucial. This includes using Digital Rights Management (DRM) technologies to control access to content and watermarks to trace the source of illegal copies.
Legal & Judicial Reform: The legal system needs to be more agile. Establishing fast-track courts specifically for copyright cases can ensure quick resolution and deter offenders.
Public Awareness: Educating the public about the real-world consequences of piracy is vital. Campaigns should highlight that piracy harms creators and can expose users to cyber threats.
Strengthened Enforcement: Law enforcement agencies, particularly cyber cells, need to be better equipped and trained to investigate and prosecute digital piracy effectively.
Promote Legal Alternatives: Encouraging the use of legitimate platforms is a key preventive measure. By offering affordable and user-friendly legal streaming services and digital stores, the industry can reduce the incentive for consumers to turn to pirated content.
Seizure and Packaging of Digitally Pirated Content
When investigating digital piracy, law enforcement follows a strict process to seize and handle evidence correctly. This ensures the evidence is legally sound for court.
Initial Steps & Search Warrant
The process begins with a formal complaint filed by the copyright holder, leading to an FIR (First Information Report) under the Copyright Act or IT Act. A search warrant is then obtained from a court, though a police officer can conduct a search without one in urgent situations if there is a strong belief that evidence will be destroyed.
Search and Seizure Protocol: The Digital Evidence Chain
The process of seizing digital evidence is far more delicate than seizing physical goods because digital data can be deleted or altered in seconds.
- Team Assembly & Legal Authority
Before the raid, a specialized team is formed. This includes:
- Investigating Officer (IO): The leader of the operation.
- Cyber Forensic Experts: To handle the technical extraction.
- Independent Witnesses (Panchas): Neutral observers who ensure the process is fair and legally documented (crucial for the Panchnama).
- Securing the Scene (The “Freeze”)
Once on-site, the team immediately secures all electronic devices.
- Rule of Thumb: If a computer is ON, leave it on; if it is OFF, leave it off.
- Connectivity: Devices are placed in “Airplane Mode” or “Faraday Bags” (special pouches that block signals) to prevent someone from remotely wiping the data via the internet.
- Search and Identification
The team identifies all potential data storage points. This isn’t just laptops; it includes:
- External Hard Drives and USB sticks.
- Cloud storage logins.
- Routers (to check internet history logs).
- Even “hidden” devices like micro-SD cards in cameras or printers.
- Forensic Data Imaging (The “Mirror Image”)
This is the most critical step. Law enforcement never works on the original device because doing so could change the metadata (like “Date Last Accessed”).
- The Tool: A “Write Blocker” is used. This device allows data to flow out of the seized drive but prevents any data from going in.
- The Result: A “Forensic Image” or “Mirror Image” is created. This is a bit-by-bit copy that includes even deleted files and hidden partitions.
- Verification (Hashing)
To prove in court that the copy is 100% identical to the original, experts use a Hash Value (a digital fingerprint).
- If even one letter in a document is changed, the “Hash Value” will completely change.
- Matching hashes prove to the judge that the evidence has not been tampered with.
- Documentation and Sealing
Every device is physically labelled, photographed, and placed in anti-static, tamper-proof packaging. The Panchnama (seizure memo) is then signed, documenting every single item taken.
Why this matters for the Law (BSA & BNSS)
Under the Bharatiya Sakshya Adhiniyam (BSA), following this protocol is what makes a digital record “admissible.” Without proper imaging and hashing, a defense lawyer can argue that the police “planted” the pirated files on the device after it was seized.
7.Chain of Custody and Forensic Analysis
The seized evidence is securely stored in an evidence locker, and a complete log of its handling is maintained to preserve its chain of custody. The devices are then sent to a Forensic Science Laboratory (FSL) or a cyber forensic expert for a detailed analysis. The expert’s report confirms the presence of pirated content, identifies the software used, and examines internet logs and other metadata.
- Write Blockers & Hashing
In a court of law, digital evidence is easily challenged because it is invisible and easy to alter. To make it “bulletproof,” law enforcement uses two specific technical tools to prove integrity:
Write Blockers (The “Shield”)
- What it is: A physical device that sits between the suspect’s hard drive and the police computer.
- What it does: It allows data to flow out (to be copied) but physically blocks any data from flowing in.
- Legal Importance: It proves to the judge that the police did not—and could not—add, delete, or “plant” any files on the original device during the investigation.
Hashing (The “Digital Fingerprint”)
- What it is: A mathematical algorithm (like SHA-256) that turns an entire drive’s worth of data into a unique string of letters and numbers (e.g., 5e884898…).
- What it does: If even a single comma or bit of data is changed on the drive, the “Hash Value” will change completely.
- Legal Importance: Under the Bharatiya Sakshya Adhiniyam (BSA), experts compare the hash of the original drive with the hash of the forensic copy. If they match perfectly, it proves the evidence is an exact, untampered “Mirror Image.”
Why this survives a Court Challenge
Without these two steps, a defense lawyer can claim that a file was accidentally modified just by the act of a police officer opening it. Write Blockers prevent the change, and Hashing proves that no change occurred.
Legal Proceedings
Following the comprehensive forensic examination, a detailed final report, synthesizing scientific findings and expert opinions, is formally submitted to the court. This critical document serves as the scientific foundation for the judicial process.
Concurrently, all seized items – ranging from physical exhibits to digital data – are rigorously maintained under strict official custody. This meticulous preservation, adhering to stringent chain of custody protocols, continues uninterrupted until the legal trial reaches its conclusion.
The unwavering commitment to maintaining their integrity ensures these items are readily available for presentation, examination, and verification as crucial evidence, safeguarding the fairness and validity of the judicial proceedings.
Conclusion
Ultimately, the Digital Forensic Investigation Process is much more than a technical routine; it is a vital safeguard for justice in an increasingly digitized legal landscape. By strictly adhering to the Chain of Custody and utilizing rigorous Evidence Preservation techniques, investigators ensure that digital artifacts—which are inherently fragile and easily manipulated—retain their integrity and “probative value” from the crime scene to the courtroom.
As technology continues to evolve, the commitment to these scientific and procedural standards remains the only way to protect the rights of the accused while ensuring that the truth remains untampered, thereby upholding the sanctity of the judicial process in the face of complex cyber challenges.